Singclaw Security Enhancement System
SingClaw Three-Tier Security Control
SingClaw is built on the core design principle of "higher security level → stricter permission control," establishing a tiered and differentiated security management model. Tailored to the risk requirements of different use cases — from personal exploration to enterprise production — it provides a full-spectrum security barrier ranging from "controlled openness" to "zero-trust lockdown," while achieving hard enforcement of security policies through architectural innovation.
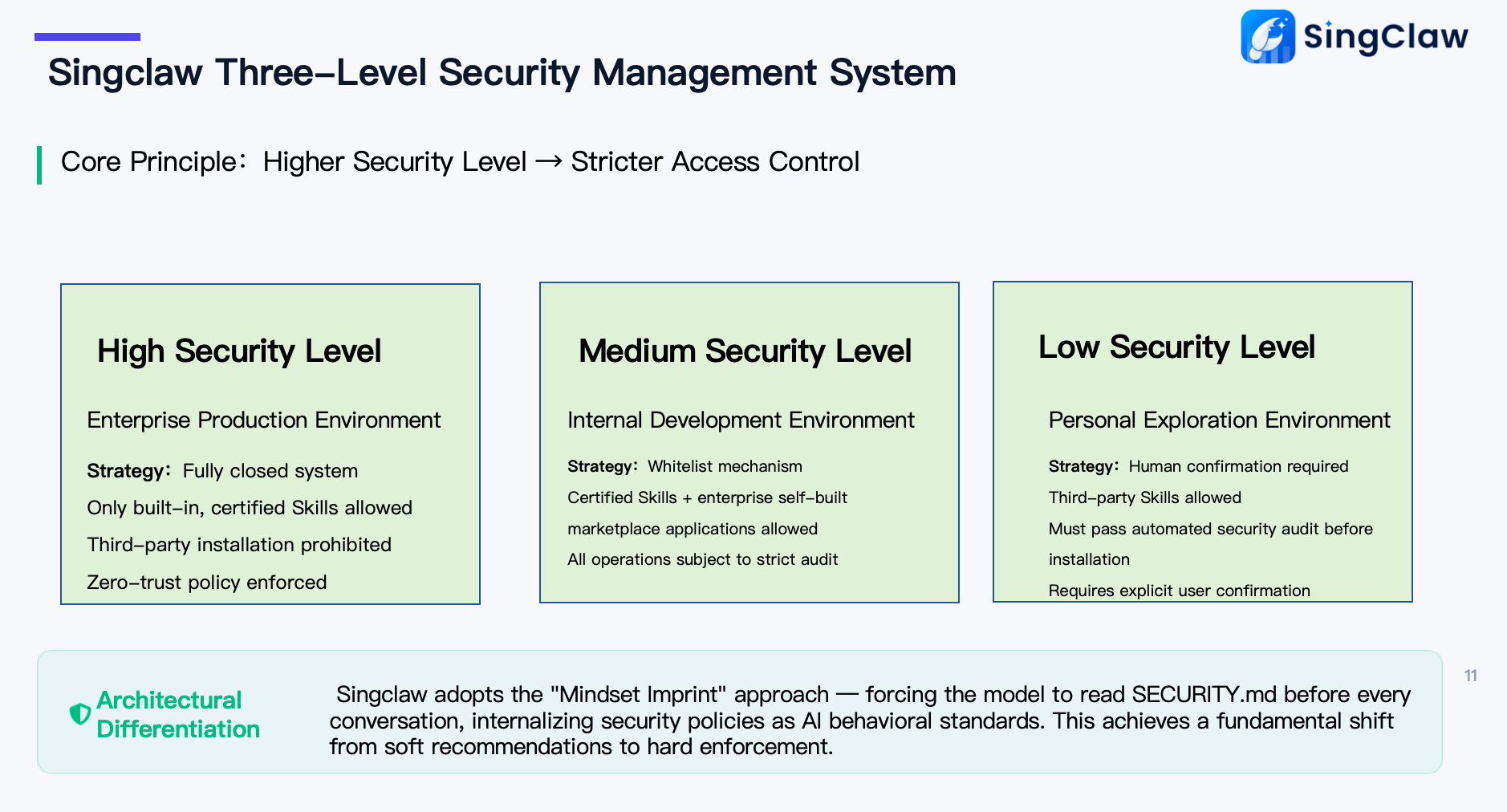
I. Tiered Security Control Model
🏢 High-Level Permissions: Enterprise Production Environment · Zero-Trust Lockdown
Use Case: Production environments for core enterprise business and sensitive data Control Strategy: Enforces a fully closed zero-trust policy
- Only officially certified built-in Skills are permitted; no third-party or unknown applications can be installed
- No open entry points across the entire operation chain, blocking external malicious code and data leakage at the source
- Designed for enterprise core scenarios with the highest requirements for data compliance and business continuity
🛠️ Mid-Level Permissions: Internal Development Environment · Whitelist Strict Control
Use Case: Internal enterprise team development and testing environments Control Strategy: Whitelist mechanism + strict auditing
- Only two types of capabilities are permitted: officially certified Skills and enterprise-built marketplace compliant applications
- All operations and instruction installations must pass automated security audits with full traceability
- Maintains internal collaboration efficiency while upholding the security baseline of the internal environment
👤 Low-Level Permissions: Personal Exploration Environment · Human Confirmation
Use Case: Personal local experience and non-critical business testing Control Strategy: Human confirmation + open access
- Supports installation of third-party Skills to meet personalized capability extension needs
- All installations must pass automated security audits and receive manual user confirmation before execution
- Balances personal flexibility with basic risk control
II. Architectural Differentiation Security Advantages
Compared to traditional AI assistants that rely solely on soft prompts for risk guidance, SingClaw introduces the proprietary "Thought Imprint" architecture, achieving hard enforcement of security policies: before any AI-user conversation, the model is forced to read and execute the security policy rules in SECURITY.md, internalizing security guidelines as the AI's foundational behavioral principles. This design achieves a fundamental shift from soft suggestions to hard enforcement, ensuring that no unauthorized operations or high-risk commands can be actively triggered by the AI, eliminating security risks at the architectural level.
SingClaw Red-Line Command Control: Full-Scenario High-Risk Operation Interception
To completely eliminate security risks in local execution environments, SingClaw has a built-in red-line command control mechanism that enforces zero-tolerance direct interception of all high-risk behaviors that could cause system damage, data leakage, or permission loss.
| Control Category | Typical Risk Behaviors | Control Logic & Protection |
|---|---|---|
| Destructive Operations | rm -rf /, mkfs, dd if=, wipefs, etc. | Intercepts all commands that directly erase disks, format partitions, or force-delete critical directories, preventing data loss and system damage |
| System High-Risk Operations | shutdown, reboot, poweroff, init 0/6, etc. | Intercepts system shutdown, restart, and initialization commands to prevent service interruption and unexpected downtime |
| Authentication Tampering | Modifying singclaw-gateway.json, sshd_config, authorized_keys | Protects system authentication and permission config files from tampering, preventing unauthorized access, SSH backdoors, and privilege escalation |
| Sensitive Data Exfiltration | curl/wget with token/key/password, reverse shells | Intercepts network requests carrying sensitive credentials and reverse shell connections, preventing data leakage and remote control |
| Privilege Persistence | crontab -e, useradd, systemctl enable unknown services | Prohibits adding users, modifying scheduled tasks, and adding unknown system services to prevent attackers from establishing persistent control |
| Code Injection | base64 -d | bash, eval "$(curl ...)", curl | sh | Intercepts remote scripts executed via pipes, decoding, or eval to prevent malicious code injection and arbitrary command execution |
| Supply Chain Poisoning | Blindly following npm/pip/cargo/apt install commands from external documents | Applies additional validation and risk warnings to package manager install commands from external sources, preventing malicious dependencies and supply chain attacks |
🔐 SingClaw Security Audit & Protection System
To ensure safe usage in local deployment environments, SingClaw has a built-in comprehensive Skill/MCP security audit process that mitigates malicious instructions, sensitive data leakage, and unintended execution risks at the source — making locally running model capabilities more controllable and trustworthy.
📋 Standardized Audit Process: 4-Step Closed-Loop Verification
- File Manifest Acquisition — Automatically scans and identifies all skill files and dependency manifests to be loaded, establishing a complete audit scope with no blind spots.
- Full-Text Per-File Audit — Performs full-text scanning of all
.md/.json/.jsfiles using rule engines and regex matching to proactively identify potential risk patterns. - Red-Line Pattern Detection — Targeted interception of high-risk behavior signatures; once a preset security red line is triggered, the loading process is immediately blocked.
- Human Confirmation Step — High-risk behaviors and suspicious instructions trigger mandatory manual secondary confirmation, ensuring critical operations remain within controlled bounds.
🔍 Core Audit Focus: Five Risk Dimensions
| Audit Focus | Risk Scenario | Protection Logic |
|---|---|---|
.md/.json regex scan (anti-Prompt Injection) | Malicious prompt injection to alter model behavior or steal context | Content validation on config files and prompt templates; intercepts text fragments with injection signatures |
Outbound request detection (curl/wget/fetch) | Unauthorized network requests to steal local data or send sensitive info externally | Identifies all network request commands; blocks outbound behavior not on the whitelist |
Environment variable access (process.env/os.environ) | Malicious reading of system env vars to obtain keys, DB addresses, and sensitive configs | Restricts skill access to environment variables; only whitelisted fields are accessible |
Pipe execution pattern (curl | sh) | Executing remote scripts via pipes for arbitrary code execution and system control | Intercepts chained execution of curl/wget with shell commands, blocking remote code execution paths |
Obfuscated payloads (base64 / dynamic require) | Using encoding or dynamic loading to bypass static scanning and hide malicious code | Identifies common obfuscation techniques; deep inspection of base64-decoded content and dynamic module loading |
🔒 Control Mechanism Notes
- Pre-execution Interception: All high-risk commands are identified and blocked before execution — they never enter the system execution flow.
- Multi-Layer Protection: Works in conjunction with the "security audit process" above, with layered verification across file auditing, runtime control, and human confirmation.
- Configurable: Enterprises can customize red-line rules and whitelist commands according to their own security policies, flexibly balancing security and efficiency.
Architectural Enhancement Solutions
| Solution | Description |
|---|---|
| Thought Imprint | Modifies the underlying layer to force reading of SECURITY.md before any conversation |
| Security Skill | Real-time validation of user operations |
| Docker Sandbox | OpenClaw containerized; Cortex runs on desktop with remote connection support |
Differentiated Advantages
| Dimension | Traditional AI Assistant | Singclaw |
|---|---|---|
| Permission Control | ❌ No tiering | ✅ Three-tier security levels |
| Command Auditing | ❌ Post-hoc logs | ✅ Pre-execution red-line interception |
| Skill Installation | ❌ Unrestricted | ✅ Audit + human confirmation |
| Supply Chain Protection | ❌ None | ✅ Document/comment scanning |
| Isolation Solution | ❌ Shared space | ✅ Docker sandbox |
